Construction Industry Webinar: From Code to Compliance – Mastering the Building Safety Act 2022
Join us for our upcoming live webinar – “From Code to Compliance: Mastering the Building Safety Act 2022” 🗓️ Date:
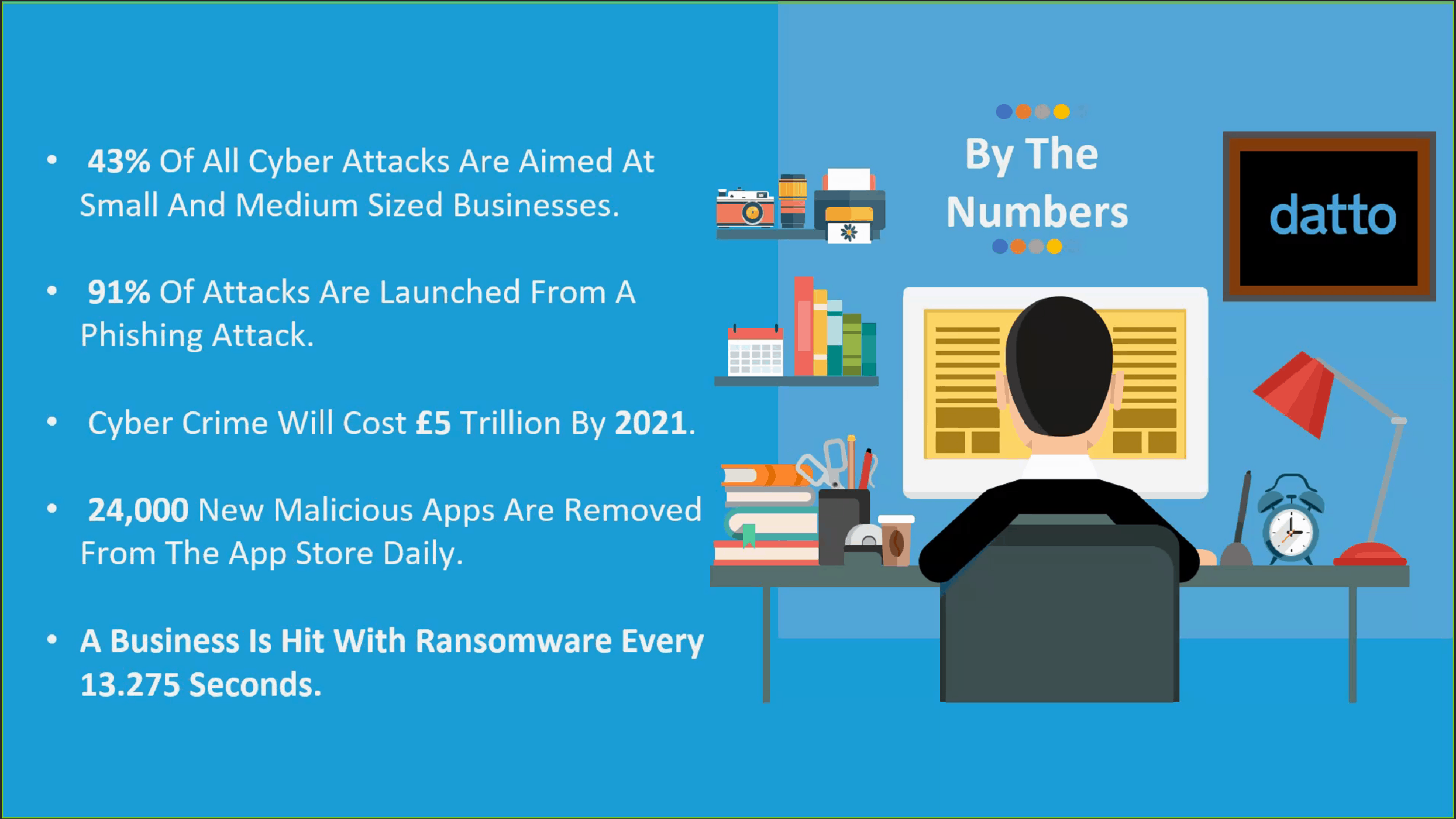
Read articleOur recent webinar, hosted by Greg Jones from Datto and Andrew Rigg from Cybit, was an exciting and eye-opening look at the current cyber security landscape that UK businesses must now face.
The key message from the webinar was that it is not just about the security systems you invest in to keep you safe – it’s about education of your staff. You need a 360 holistic strategy to cover you from any human errors.
Cyber crime is at record high levels due to the rise in remote working – and it isn’t likely to go anywhere. SMBs often think they’re too small or not important enough to be attacked – but it’s not the case.
There are many ways to hack a company. We’ve seen people been hacked through a cleaner putting a memory stick into the back of a PC – or even via a Wi-Fi powered kettle.

Based on your industry they will know the busiest time, for example during payroll or financial end of year, so that when they email you it gets caught up in the other hundreds of emails you will receive during that time and go unnoticed.
A Las Vegas casino suffered a massive breach when hackers, in the casino’s foyer, hacked into the digital thermostat in the fish tank to access the casino’s network. From there they gained access to the casino’s private databases and systems that was then shared online with other cyber criminals.

Organisations think that by using cloud suites, like G Suite or Microsoft 365 (formerly Office 365), that data is secure and protected against attack. But Microsoft and Google both state that data should be backed up by a third party.
SaaS Protection covers your Google data including Gmail, calendar, contacts, Google Drive. For Microsoft this covers Teams, OneDrive, SharePoint, emails, and calendar.
All of your organisation’s data is backed up 3 times a day. Backing up your data gives you 100% peace of mind that if anything happens we can roll your data back to a snapshot in time. You’re back up and running in minutes.
We received many questions during the webinar and we’ve selected the best here for you:
Q: Does SaaS Protection back up Microsoft Teams?
Greg: It backs up Teams drives – individual Teams conversations is coming as part of the SaaS Protection roadmap. You will get that. The product is being updated monthly with the latest features.
Andrew: As Microsoft releases access to their APIs, this changes how deep we can go into protecting data.
Q: A stat recently said 60% of SMBs go out of business after a cyber attack
Andrew: The problem is that businesses might have business continuity or disaster recovery for parts of their business – not all of it.
Greg: You need documented plans and procedures in place for what to do if an attack should happen. Cybit can give you advice about how to create a strategy. If your business goes blind overnight and you lose all data, how hard will that be on you from a reputation and financial point of view?
Q: Will ransomware infect recycle bins?
Greg: The first thing hackers do is look for backups of your data and delete them. They get rid of files from the recycle bin, change file names, anything so you can’t recover data. You can buy hacking tools for less than £100 online and go to an app store, download whatever malicious software you want to run on someone’s network. We’re all very vulnerable unless you take a 360-degree approach to this.
Q: Can we improve the secure score for Microsoft 365?
Greg: Regularly check your systems. With remote working, have you moved to new IT tools quite rapidly? Your team might not be quite up to speed on it yet. But make sure you’re engaging with Cybit for a health check or chat around how to secure working from home.
I can’t stress enough how important educating your staff is. For any organisation what sits between the front of the keyboard and the back of the chair is your biggest risk – your employees. They’re already in your network, they might just click a link or have been targeted for months to gain access.
Andrew: You may not be immediately attacked. For months a hacker will assess your business before they attack.
Greg: It’s normally around 180 days they’ll stay dormant within your network before they strike. People can plug in malicious USB drives at conventions, or give them away at events. They’re extremely intelligent and sophisticated.
Q: Are hackers starting to use AI technology to customise attacks?
Greg: Some things we can’t go into for legal reasons. But AI is being used to try new algorithms that’ll be handed over to a human once a vulnerability has been found.
Protecting your IT is something that needs constant effort. You can’t just focus on it for a month and be satisfied, you (or your IT partner) needs to constantly assess your IT infrastructure to see whether you’re ahead of the curve and protected.
We understand there are many options to choose from and you want to make sure the tool you adopt is the right one for you.
"*" indicates required fields
Construction in Crisis! Written by Chrissie McAnelly, Cybit Data & Analytics Consultant – Construction Sector The construction sector is
Read articleBy Asiel Esgair – Cybit Data & Analytics Consultant – Public Sector & Local Authority In our
Read article